A survivor in a basement apartment checks her phone for the third time tonight. No alerts — but that might mean the system is working, or it might mean her ex-husband found a cellular dead zone three blocks away and is approaching undetected. For her, the difference between those two scenarios is the difference between safety and a hospital visit.
This is not a hypothetical. In Western Australia, the Department of Justice declared GPS monitoring of DV offenders in regional areas “not feasible” due to cellular black spots (ABC News, April 2025). In Quebec, advocates warned that monitoring bracelets fail in remote communities because exclusion zones that work in cities generate constant false alerts in small towns with single roads (CBC News, 2024). In Tennessee, offenders walked free for 14 to 30 days after court-ordered monitoring because of paperwork errors and sheriff’s office coordination failures (WSMV, November 2024).
These are not edge cases. They are systemic failures rooted in the technology architecture of most GPS ankle monitors currently deployed for domestic violence protection. And they share a common root cause: devices designed for general offender supervision being repurposed for the most demanding application in electronic monitoring — where a single missed proximity alert can result in serious injury or death.
This guide is written for two audiences. If you are drafting RFP requirements for a DV GPS monitoring program, every technical specification discussed here belongs in your evaluation criteria. If you are an EM service provider looking for equipment that actually works in DV protection, the performance benchmarks in this article are the minimum threshold your hardware must clear.
Why Domestic Violence Monitoring Is the Hardest Application in Electronic Monitoring
Standard offender monitoring — curfew compliance, geographic restriction, probation check-ins — tolerates a certain margin of error. A 5-minute reporting gap during routine supervision is an inconvenience. A 5-minute reporting gap during a protection order violation can be a fatality.
DV monitoring imposes five technical demands that most general-purpose GPS ankle monitors cannot reliably satisfy:
| Requirement | Why It Matters in DV | What Most Devices Actually Deliver |
|---|---|---|
| Sub-5m GPS accuracy | An exclusion zone breach alert triggered at 50 meters instead of 300 meters gives the victim seconds, not minutes, to react | 3-10m CEP; degrades to 50-100m indoors |
| Zero-gap continuous tracking | Any monitoring blackout — cellular dead zone, building interior, rural coverage gap — is a window of opportunity for the offender | LTE-only connectivity; 100% dependent on cellular coverage |
| Zero false-positive tamper alerts | Each false tamper alert dispatches officers, traumatizes the victim with fear, and erodes the court’s confidence in the technology | PPG/heart-rate sensors produce 15-30% false-positive rates |
| Multi-day battery without charging gaps | Every charging session is a monitoring gap. A DV offender who “forgets” to charge creates an unmonitored window | 24-72 hours typical; daily charging required |
| Victim-side protection mechanism | The offender’s device alone is insufficient — the victim needs independent alerting, panic capability, and real-time awareness | Most systems offer no victim-side device or app; rely on monitoring center callbacks |

The Five Failure Modes That Kill DV Monitoring Programs
Before discussing solutions, agencies need to understand exactly why existing deployments fail. Each failure mode corresponds to a specific architectural limitation in legacy GPS ankle monitors.
Failure Mode 1: The Cellular Dead Zone Problem
Every GPS ankle monitor on the market from established vendors — SCRAM, BI Incorporated, Geosatis, SuperCom, Track Group — relies exclusively on LTE/3G cellular connectivity to transmit location data. When the offender enters an area with weak or no cellular coverage, the device stores location data locally but cannot transmit alerts in real time.
For routine supervision, this produces a delayed data dump when connectivity resumes. For DV protection, it means an offender can approach a victim’s location while the monitoring center receives nothing.
This is not a rare occurrence. The FCC’s 2024 Broadband Progress Report estimates that 21% of rural Americans lack adequate mobile broadband coverage. In Western Australia, authorities officially declared DV GPS monitoring “not feasible” in regional areas because of this exact gap (ABC News, 2025). In Quebec, remote communities on the North Shore lack the cellular infrastructure to make bracelets reliable (CBC, 2024).
Failure Mode 2: The Battery-Charging Vulnerability
Legacy one-piece GPS ankle monitors — running continuous GNSS positioning and LTE transmission — deplete their batteries in 24 to 72 hours. This means the offender must charge the device daily, creating a predictable monitoring gap during each charging session.
For DV cases, this gap is a calculated opportunity. An offender who deliberately “forgets” to charge generates a low-battery alert that looks identical to a compliance failure — the monitoring officer cannot distinguish deliberate evasion from carelessness. Meanwhile, during the time between the low-battery alert and physical intervention, the device may lose tracking capability entirely.
A 500-person caseload typically generates 50-100 low-battery alerts per day. At an estimated $15 per alert in officer response time, that represents $273,000/year in operational cost — and each alert is a potential moment of vulnerability for the victim.
Failure Mode 3: Tamper Detection False Positives
Traditional tamper detection relies on PPG (photoplethysmography) skin-contact sensors or resistive/capacitive circuit monitoring. These technologies produce 15-30% false-positive rates under real-world conditions — sweat, dry skin, movement during exercise, and temperature changes all trigger false tamper alerts.
In DV cases, false tamper alerts are catastrophic for two reasons. First, they desensitize monitoring officers to tamper warnings, creating a “boy who cried wolf” effect that delays response to genuine removal attempts. Second, defense attorneys routinely use documented false-positive rates to challenge the reliability of GPS evidence in court, undermining the very protection the device is supposed to provide.
Failure Mode 4: Inflexible Exclusion Zone Configuration
Most monitoring platforms offer fixed-radius geofences around static locations. A DV victim’s home gets a 500-meter exclusion zone. The victim’s workplace gets another. The children’s school gets a third.
Real life is not this simple. The victim moves between locations throughout the day. She visits a friend’s house. She takes a different route to work. In Quebec, advocates pointed out that small communities with single roads made it impossible to configure exclusion zones that did not overlap with the offender’s only route to essential services — generating constant false alerts that rendered the system useless (CBC, 2024).
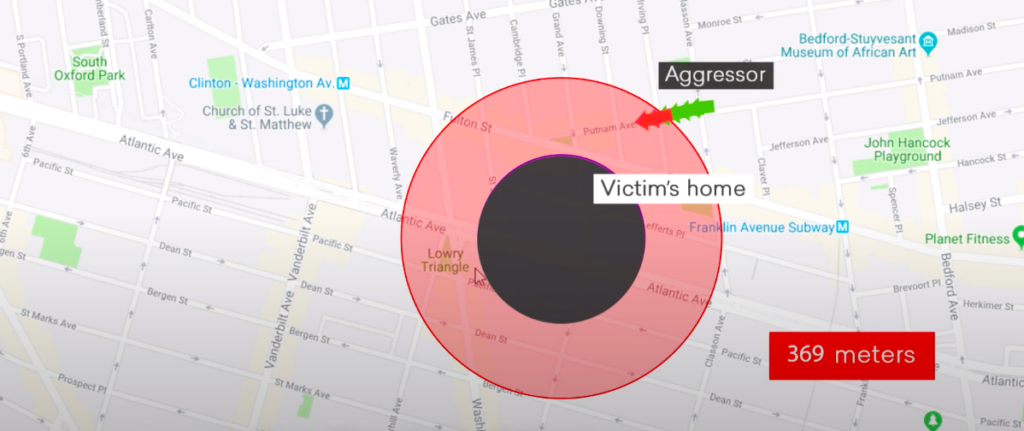
What DV programs actually need is a multi-tier zone architecture: an outer early-warning perimeter (e.g., 500m) that escalates to a critical inner zone (e.g., 100m), combined with mobile zones that follow the victim’s real-time location — not just fixed points on a map.
Failure Mode 5: No Victim-Side Protection
The most fundamental design flaw in conventional DV GPS monitoring: the system tracks the offender but provides no independent protection mechanism for the victim.
When an exclusion zone is breached, the alert goes to the monitoring center. The monitoring center calls the victim — if she answers. If she does not answer (because she is sleeping, driving, or already being confronted), the center escalates to law enforcement. This chain of communication introduces minutes of delay into a situation where seconds matter.
A National Institute of Justice evaluation study found that only one-third of law enforcement agencies using electronic monitoring actually utilized alert systems for survivors. The majority relied on monitoring-center-to-victim phone calls — a mechanism that fails precisely when it is needed most.
How to Design a DV GPS Monitoring System That Actually Works
Fixing these five failure modes requires a fundamentally different technical architecture — not incremental improvements to legacy devices. Here is the design blueprint.

Design Principle 1: Multi-Mode Connectivity Eliminates Dead Zones
The cellular dead zone problem is unsolvable within a cellular-only architecture. The solution is to add redundant communication pathways that function independently of cellular coverage.
CO-EYE ONE-AC implements an industry-first adaptive multi-mode connectivity engine with three independent communication channels:
| Mode | How It Works | Battery Life | DV Application |
|---|---|---|---|
| BLE Connected | Encrypted BLE link to victim’s or officer’s smartphone (AMClient app) or HouseStation — offloads GNSS/LTE processing | 180 days | Offender at home or in proximity to any BLE relay device |
| WiFi Directed | Auto-connects to configured WiFi access points — transmits data through existing WiFi infrastructure | 20 days | Basement apartments, rural homes with WiFi but no cell coverage — a $10 WiFi repeater eliminates the dead zone |
| LTE Standalone | Full autonomous GNSS + LTE tracking when BLE/WiFi unavailable | 7 days | Outdoor movement, away from all infrastructure |
The device switches between modes automatically, with zero human intervention. When the offender enters a building with WiFi but no cellular coverage, the device seamlessly transitions from LTE to WiFi-directed mode. When the offender is at home with a phone running AMClient nearby, it drops to ultra-low-power BLE mode.
For the DV use case, this means: there is no scenario where the device simply stops reporting because of infrastructure limitations. The offender cannot exploit a dead zone because the device has three independent pathways to maintain connectivity.
Design Principle 2: Battery Architecture That Closes the Charging Gap
The battery problem in legacy devices is architectural, not chemical. Running continuous GNSS + LTE at full power drains any reasonably-sized battery in 24-72 hours. CO-EYE ONE-AC solves this at the system level: by offloading heavy processing to companion devices via BLE during indoor periods (which account for 80-90% of monitoring time), the ankle device operates at a fraction of the power consumption.
The operational impact for DV programs:
- BLE mode (180 days): When the offender is at home or work with a phone nearby, the device runs for six months on a single charge. The charging management problem effectively disappears.
- WiFi mode (20 days): Even without BLE, WiFi-directed operation extends battery to three weeks — reducing charging from daily to biweekly.
- LTE standalone (7 days): In the worst case, with no WiFi or BLE available, the battery lasts a full week — 2-7x longer than any competing device.
For DV monitoring officers, this translates to an estimated 85% reduction in charging-related alerts and a near-elimination of the “deliberate low-battery” evasion tactic.
Design Principle 3: Fiber-Optic Tamper Detection — Binary, Not Probabilistic
The tamper detection problem is fundamentally a signal-processing problem. PPG and resistive sensors produce analog signals with inherent noise — the system must decide whether a change in signal represents genuine tamper or environmental interference. This probabilistic judgment produces the 15-30% false-positive rates that destroy DV monitoring credibility.
Fiber-optic tamper detection is binary. A continuous optical fiber loop runs through both the strap and the device case. Light either passes through the loop or it does not. There is no ambiguous middle state. A genuine tamper (cutting, stretching, or removing the strap) physically interrupts the fiber — producing a definitive, unambiguous signal.
For DV applications, the implications are immediate:
- Zero false-positive tamper alerts — every tamper alert is real, and officers respond accordingly
- Court-grade evidence — defense attorneys cannot challenge fiber-optic detection with “but the device also triggers when the defendant sweats”
- 3-month post-battery tamper protection — even after complete battery depletion, the fiber-optic loop retains physical evidence of any tamper attempt. No competing technology offers this capability.
- Optional steel-armed strap — for high-risk DV cases involving strangulation or weapon charges, a steel-reinforced fiber-optic strap resists cutting with ordinary tools
Design Principle 4: Multi-Tier Exclusion Zones with Mobile Victim Tracking
A properly designed DV monitoring platform must go beyond fixed-radius geofences. The CO-EYE monitoring software supports a layered zone architecture:
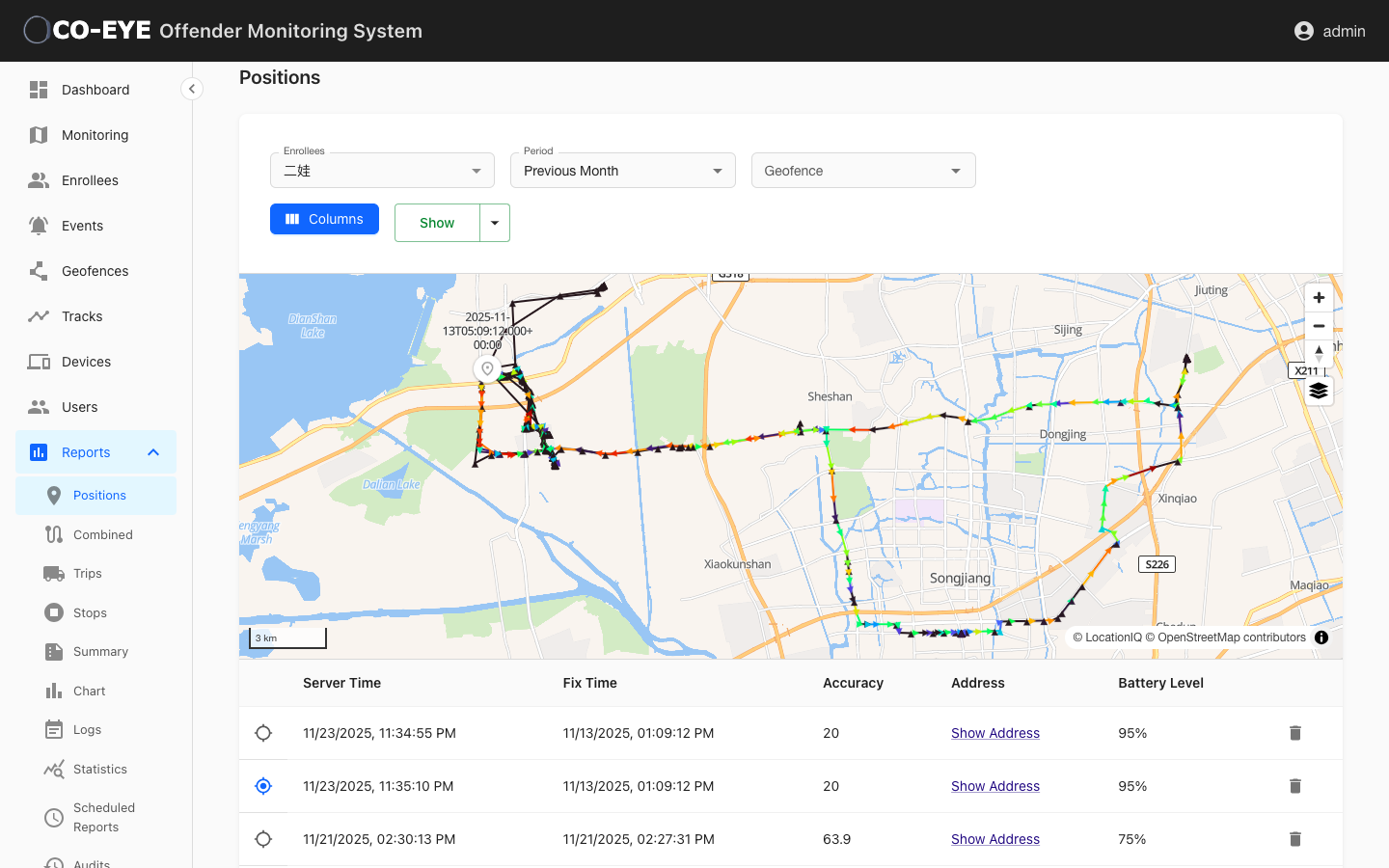
Fixed exclusion zones around known protected locations (victim’s home, workplace, children’s school, shelter) with configurable radii. Each zone supports multi-tier configuration:
- Outer warning zone (e.g., 500m): Generates an early-warning alert to the monitoring center and victim
- Inner critical zone (e.g., 100m): Triggers immediate escalation — automated victim notification, law enforcement dispatch, all notification channels activated simultaneously
Mobile exclusion zones that follow the victim’s real-time GPS position through the AMClient app installed on the victim’s smartphone. This means the protection perimeter travels with the victim — not just her home address.
Inclusion zones for offender confinement — house arrest boundaries, work release corridors, approved travel routes — with automatic alerts when the offender leaves authorized areas.
Calendar-based curfew enforcement using iCalendar format for time-of-day restrictions, with different zone configurations for weekdays vs. weekends, work hours vs. evening hours.
The platform pushes alerts through every available channel simultaneously: web dashboard, email, SMS, push notification, Telegram, and WhatsApp — ensuring the victim receives the alert regardless of which communication method she has available at that moment.
Design Principle 5: Victim-Side Protection — AMClient Changes the Economics
Traditional bilateral EM (BEM) systems — used in Spain, Portugal, and some US jurisdictions — require the victim to carry a dedicated GPS device. This doubles the hardware cost, creates a logistics burden (the victim’s device also needs charging and maintenance), and introduces another point of failure.
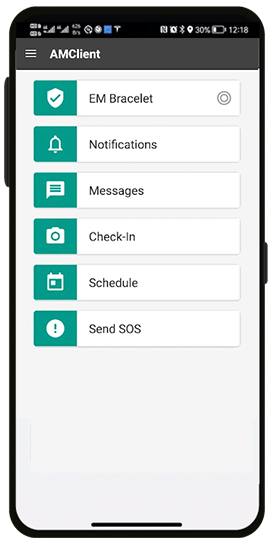
The CO-EYE AMClient app reimagines victim protection by leveraging the device every survivor already carries: her smartphone.
How AMClient works for DV victim protection:
- Free, zero-cost deployment — no additional hardware purchase. The app installs on any iOS or Android smartphone the victim already owns. This eliminates the $200-400/device cost of dedicated victim GPS units and removes any financial barrier to deploying victim-side protection.
- Continuous background GPS tracking — the app tracks the victim’s location even when the screen is off, enabling mobile exclusion zones that follow her real-time position
- Panic SOS button — one-tap emergency alert that simultaneously notifies the monitoring center, law enforcement, and designated emergency contacts with the victim’s current GPS coordinates
- Push notifications — instant alerts when the offender approaches any exclusion zone, giving the victim time to secure her location or evacuate
- BLE proximity detection — when the offender’s CO-EYE ONE ankle monitor comes within BLE range (up to 60 meters in open space), the AMClient app on the victim’s phone detects the BLE signal and triggers an immediate proximity alert — even in areas with no cellular or GPS coverage. This is the last line of defense in cellular dead zones.
- Check-in with photo verification — the victim can confirm her safety status at scheduled intervals, and the system flags missed check-ins for follow-up
- Multi-channel notifications — alerts reach the victim through push notification, SMS, email, Telegram, and WhatsApp — whichever channel is available in her current environment
- Family/advocate deployment — the app can also be installed on smartphones of the victim’s family members, friends, or advocates, creating a distributed protection network around the survivor. Multiple phones running AMClient multiply the BLE detection coverage and ensure someone in the victim’s support circle receives every alert.
For RFP writers: the ability to deploy victim-side protection at zero marginal hardware cost per victim fundamentally changes the economics of DV GPS programs. A jurisdiction that might only afford to protect 50 victims with dedicated hardware devices can now protect 500 by leveraging smartphones. AMClient is available on both Apple App Store and Google Play.
What RFP Writers Miss: The Technical Specifications That Separate Real DV Protection from Vendor Theater
Most RFPs for DV GPS monitoring programs are written by procurement officers adapting general EM requirements. They specify “GPS tracking” and “geofencing” — but miss the DV-specific technical requirements that determine whether the system actually protects victims.
Include these specifications in your next evaluation:

| RFP Specification | Why Standard EM Specs Are Insufficient | What to Require for DV | CO-EYE Capability |
|---|---|---|---|
| GPS Accuracy | Standard EM: “GPS tracking.” DV needs precision for proximity alerting | < 5m CEP (outdoor), with WiFi/LBS indoor fallback | < 2m CEP (4-constellation GNSS) |
| Connectivity Redundancy | Standard EM: “Cellular communication.” DV cannot tolerate dead zones | Minimum 2 independent communication channels | 3 channels: BLE + WiFi + LTE-M/NB-IoT |
| Battery Life | Standard EM: “Rechargeable.” DV needs minimized charging gaps | > 5 days standalone; BLE/WiFi extended modes preferred | 7 days LTE / 20 days WiFi / 180 days BLE |
| Tamper Detection FPR | Standard EM: “Tamper alerts.” DV needs zero false positives for court credibility | < 1% false-positive rate (fiber-optic preferred) | 0% (fiber-optic binary detection) |
| Victim Notification | Standard EM: not required. DV mandates real-time victim alerting | Multi-channel automated victim notification within seconds of zone breach | Push + SMS + Email + Telegram + WhatsApp |
| Victim-Side Device | Standard EM: offender-only. DV needs bilateral protection | Smartphone-based victim app with GPS, BLE proximity, and SOS | AMClient (free, iOS/Android) |
| Mobile Exclusion Zones | Standard EM: fixed geofences. DV victims are mobile | Dynamic zones following victim’s real-time GPS | AMClient mobile zone tracking |
| Installation Speed | Standard EM: field installation. DV needs courtroom-ready deployment | < 5 minutes total, no specialized tools | 3-second snap-on, pre-sized S/M/L/XL straps |
| Network Future-Proofing | Many agencies still use 3G devices facing sunset | 5G-compatible cellular (LTE-M/NB-IoT) | LTE-M/NB-IoT + eSIM + Nano SIM |
| Cybersecurity Certification | DV location data is highly sensitive — misuse or breach can endanger the victim | Independent security certification | EN 18031 cybersecurity certified |
The Pitfalls Agencies Discover After Deployment — and How to Avoid Them
Even agencies that choose technically competent equipment can sabotage their DV programs through operational design errors. Here are the most common post-deployment failures and their solutions.
Pitfall 1: Single-Channel Victim Notification
If victim alerts only go through push notifications, a victim with a dead phone battery receives nothing. If alerts only go through SMS, a victim in a no-service area receives nothing. The solution: configure every victim for multi-channel simultaneous notification — push, SMS, email, Telegram, WhatsApp, and monitoring-center voice call — so at least one channel reaches her regardless of circumstances.
Pitfall 2: Exclusion Zones Too Tight for Rural Communities
In Quebec, advocates found that 500-meter exclusion zones in small communities with single roads generated constant false alerts because the offender’s only route to work passed within the zone. The solution: use multi-tier zones (outer warning at 500m, critical at 100m) so officers can distinguish “offender is in the general area” from “offender is approaching the victim’s door.” Adjust zone radii based on local geography — not a one-size-fits-all national template.
Pitfall 3: No Protocol for Overnight Dead-Battery Alerts
A low-battery alert at 2 AM generates a notification, but the on-call officer may not act until morning — by which time the device may be dead and the offender is unmonitored. The solution: equipment with 7+ day battery life reduces these events by 85%. For the remaining cases, establish mandatory escalation timelines: if the offender does not begin charging within 2 hours of a low-battery alert, law enforcement is dispatched regardless of time of day.
Pitfall 4: Treating the Monitoring Center as a Phone Tree
Many agencies route all alerts through a monitoring center that then manually calls the victim, the officer, and law enforcement — sequentially. In a critical proximity breach, this sequential notification can add 5-10 minutes of delay. The solution: configure automated simultaneous notifications to all stakeholders the moment a critical zone is breached. The monitoring center should escalate, not relay.
Pitfall 5: No Court-Ready Evidence Package
When a protection order violation is detected, the prosecution needs timestamped GPS tracks, zone breach logs, tamper history, and device status records — packaged in a format that withstands courtroom challenge. If this reporting must be assembled manually from raw data, it delays proceedings and introduces transcription errors. The solution: the monitoring platform must support one-click generation of court-evidence packages with GPS track playback, timestamped breach records, and certified device integrity logs.
The Complete CO-EYE DV Solution: One Platform, Full Coverage, Zero Additional Victim Hardware Cost
Here is how the complete solution maps to a DV protection deployment:
| Component | Role | Key DV Feature | Cost Model |
|---|---|---|---|
| CO-EYE ONE / ONE-AC | Offender ankle monitor | 3-mode connectivity, 7-180 day battery, < 2m accuracy, fiber-optic zero-FP tamper, 108g | Per-device hardware |
| CO-EYE Monitoring Software | Central management platform | Multi-tier geofences, calendar curfew, real-time maps, automated multi-channel notifications, court-evidence reporting | Platform license |
| AMClient App | Victim protection | Mobile exclusion zones, BLE proximity detection, panic SOS, multi-channel alerts, family deployment | Free (no hardware cost) |
| HouseStation (optional) | Offender home monitoring | Enhanced BLE range (50m indoor), dual-SIM phone, power-outage battery backup | Per-unit (optional add-on) |
| WiFi Repeater (optional) | Dead zone elimination | Enables WiFi-directed mode in basements/rural homes without cellular coverage | ~$10 (consumer-grade) |
The total cost structure: one professional ankle device per offender, one free smartphone app per victim (and her support network), and a monitoring platform. No dedicated victim hardware. No base stations required. No specialized installation tools. An officer can deploy a complete DV monitoring setup — from ankle strap to exclusion zone configuration to victim notification testing — in under 30 minutes.
What Happens When the Offender Approaches: A Step-by-Step Scenario
To make this concrete, here is exactly what happens when a monitored DV offender violates an exclusion zone using the CO-EYE system:
- Offender crosses outer warning zone (500m) — CO-EYE ONE detects the offender’s GPS position within the 500m perimeter. The monitoring platform generates an early-warning alert. The victim’s AMClient app displays a push notification: “Warning: monitored person approaching your area.” The monitoring center receives the alert on their dashboard.
- Offender continues toward critical zone (100m) — Alert escalation. Automated notifications fire simultaneously through all configured channels (push, SMS, email, Telegram, WhatsApp) to the victim, the supervising officer, and designated emergency contacts. The monitoring center initiates the law enforcement dispatch protocol.
- Offender’s BLE signal detected by victim’s phone — If the offender comes within 60 meters and the victim’s phone is running AMClient, BLE proximity detection triggers an immediate alarm — this works even in areas with no cellular or GPS coverage, because BLE is a direct device-to-phone signal.
- Victim activates SOS — One tap on the AMClient SOS button sends the victim’s exact GPS coordinates to the monitoring center, law enforcement, and all emergency contacts simultaneously.
- Evidence capture — Throughout this entire sequence, the CO-EYE platform records timestamped GPS positions, zone breach events, BLE proximity detections, notification delivery confirmations, and SOS activations — generating a complete, court-admissible evidence package.
Every step is automated. No manual phone calls. No sequential notification chains. No single points of failure.
Frequently Asked Questions
What GPS accuracy is required for domestic violence exclusion zone monitoring?
DV exclusion zones require sub-5-meter GPS accuracy to differentiate between an offender near a boundary versus inside a protected zone. CO-EYE ONE achieves less than 2 meters CEP using four-constellation GNSS (GPS, BeiDou, GLONASS, Galileo), with WiFi and LBS fallback for indoor environments where satellite signals degrade.
How does the system work when there is no cellular coverage?
CO-EYE ONE-AC maintains monitoring through three independent connectivity channels. In areas without cellular coverage, the device automatically switches to WiFi-directed mode (if a WiFi network is available) or BLE-connected mode (if a smartphone or HouseStation is nearby). A consumer-grade WiFi repeater placed in a basement or rural home costs approximately $10 and restores full monitoring capability. BLE proximity detection between the offender’s device and the victim’s AMClient app works independently of all external infrastructure.
What is the false alarm rate for tamper detection in DV GPS ankle monitors?
Traditional GPS ankle monitors using PPG or resistive tamper sensors produce 15-30% false-positive rates. CO-EYE ONE uses fiber-optic tamper detection with a zero false-positive rate — the optical fiber either conducts light (intact) or does not (tampered). This binary detection eliminates the false alarm problem that erodes both officer response urgency and courtroom evidence credibility.
Can the victim receive alerts without carrying a separate GPS device?
Yes. The CO-EYE AMClient app installs on any iOS or Android smartphone the victim already owns, at no cost. It provides real-time proximity alerts, push notifications for exclusion zone breaches, BLE-based proximity detection (up to 60m range), and a one-tap SOS panic button. The app can also be installed on family members’ phones, creating a distributed protection network without any additional hardware.
How quickly can the system be deployed after a protection order is issued?
CO-EYE ONE installs in under 3 seconds with a tool-free snap-on mechanism. Pre-sized straps (S/M/L/XL) eliminate fitting delays. An officer can complete the full deployment — device installation, exclusion zone configuration, victim app setup, and notification testing — in under 30 minutes. This enables same-day deployment during a protection order hearing.