How Do GPS Ankle Monitors Enforce Domestic Violence Protection Orders?
GPS ankle monitors enforce domestic violence protection orders by creating virtual geographic boundaries — exclusion zones — around locations the offender is legally prohibited from approaching. The device continuously reports its GPS coordinates, and when those coordinates enter a restricted area, the monitoring platform triggers alerts to supervision staff, law enforcement, and often the victim directly. This mechanism transforms a paper court order into an actively monitored, technology-enforced boundary with a documented evidence trail.

The Protection Gap That GPS Monitoring Addresses
A protection order without monitoring is a legal document. It tells the offender to stay away, and imposes criminal penalties if they don’t. But the victim has no way to know whether the offender is complying — or approaching — until a violation occurs in person. The National Institute of Justice noted that traditional protection orders are “only as effective as the offender’s willingness to comply,” and violation rates range from 23% to 70% depending on the study population and jurisdiction.
RF (radio frequency) monitoring, the older and cheaper technology, partially addresses this gap. An RF ankle transmitter paired with a home base station can confirm that the offender is at their own residence during curfew hours. But RF cannot detect where the offender goes when they leave home. If a DV offender subject to a protection order drives to the victim’s neighborhood at 2 PM on a Tuesday — well outside curfew hours — an RF system has no idea.
GPS monitoring closes this gap entirely. The device tracks the offender’s real-time location 24 hours a day, regardless of whether they’re home or not. Exclusion zones can be placed around the victim’s home, workplace, children’s school, a shelter, or any other location specified in the court order.
How Exclusion Zone Enforcement Works — Step by Step
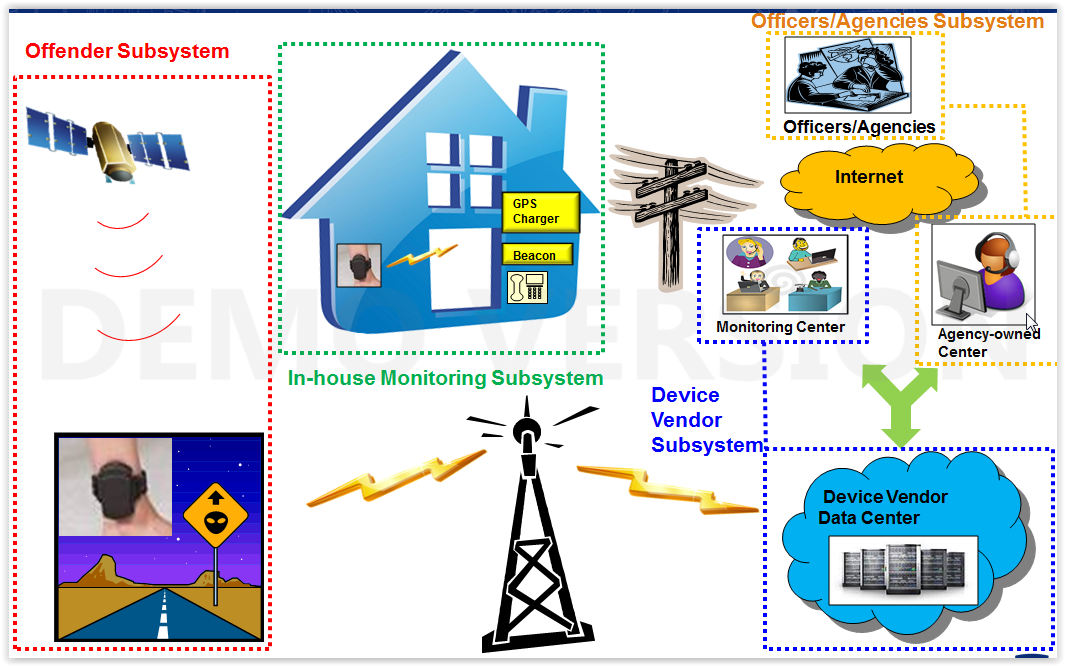
When a court orders GPS monitoring as a condition of a DV protection order, the supervising agency configures the monitoring system through several steps:
1. Zone Definition
An officer enters the protected locations into the monitoring software. Each location gets a circular or polygon-shaped exclusion zone with a configurable radius. Most agencies use two concentric zones:
- Outer warning zone — typically 500 meters to 1 mile. Entering this zone generates a lower-priority alert to the monitoring center.
- Inner critical zone — typically 150 to 500 meters. Entering this zone triggers immediate law enforcement notification and victim alert.
2. Continuous GPS Reporting
The ankle monitor records its position at regular intervals. For DV cases, most agencies configure reporting every 1 to 5 minutes over LTE-M or NB-IoT cellular networks. Some devices also use Wi-Fi positioning as a fallback when GPS satellite signals are blocked by buildings — a common scenario in apartment complexes where many DV situations occur.
3. Alert Generation
The monitoring platform compares each incoming GPS coordinate against all active exclusion zones for that offender. When a coordinate falls inside a zone boundary, the system generates an alert classified by severity level. The alert includes the offender’s current location, speed of approach, and direction of travel.
4. Escalation Response
Monitoring center staff follow a predefined response protocol. For outer-zone alerts, the standard response is to call the offender and instruct them to leave the area. For inner-zone alerts, the response escalates to law enforcement dispatch and direct victim notification. The entire sequence from GPS coordinate receipt to victim notification typically occurs within 60 to 120 seconds.
5. Evidence Documentation
Every GPS coordinate, zone entry/exit event, and alert response is logged with timestamps. This creates court-admissible evidence for violation hearings. Unlike a witness statement that can be challenged on reliability, GPS trail data provides objective documentation of exactly when the offender entered the restricted area, how close they got, and how long they remained.
GPS vs RF: Why GPS Is Required for DV Cases
| Capability | GPS Ankle Monitor | RF Home Unit |
|---|---|---|
| Exclusion zone enforcement | Yes — multiple zones, any location | No — only detects home presence |
| Real-time location tracking | Yes — continuous 24/7 | No — home or away only |
| Court-admissible location trail | Yes — timestamped coordinates | No — only curfew compliance data |
| Victim proximity detection | Yes — distance from protected locations | No |
| Victim notification capability | Yes — paired with smartphone app | No |
| Indoor tracking fallback | Wi-Fi + cellular LBS | N/A |
| Typical cost per day | $5–15 | $2–5 |
The NIJ’s evaluation study of GPS monitoring technologies in DV cases concluded that GPS provides “significantly greater protective capability” than RF for protection order enforcement. The cost difference of $3–10 per day is marginal compared to a single law enforcement response to a DV incident, which averages $2,000–5,000 including officer time, report filing, and potential hospital transport.
What Makes a GPS System Effective for DV Specifically?
Not all GPS ankle monitors perform equally in DV applications. Features that matter most for victim protection:
- Alert speed: The time from zone entry to alert generation should be under 60 seconds. Systems that batch GPS uploads every 15-30 minutes are inadequate for DV monitoring.
- Tamper resistance: DV offenders are highly motivated to remove the device. Optical fiber anti-tamper straps provide deterministic cut detection — either the fiber is intact or it’s severed, with no ambiguity. Heart-rate-based tamper detection generates false alarms that can desensitize monitoring staff. One-piece devices like the CO-EYE ONE integrate GPS, cellular, and anti-tamper in a single unit, eliminating the communication failure between separate tracker and bracelet components.
- Victim-side technology: A paired smartphone application — such as the CO-EYE AMClient App — provides the victim with independent alerts and a panic SOS button, rather than relying entirely on the monitoring center’s response time.
- Indoor positioning: Many protection order violations occur at indoor locations (apartment buildings, shopping malls, workplaces). Wi-Fi and cellular LBS fallback positioning prevents the “GPS blackout” inside buildings that could allow an offender to approach undetected.
Related Resources
- Domestic Violence Electronic Monitoring: A Technology and Implementation Guide — comprehensive program planning guide
- GPS Exclusion Zones: Configuration and Best Practices — technical deep dive on zone setup
- CO-EYE Domestic Violence Solutions — product specifications for DV monitoring
- GPS Ankle Monitor Buyer’s Guide — comprehensive technology comparison




